With the rapid rise of remote work, companies and employees have been forced to adapt to a new way of doing business. While this shift has brought about numerous benefits, it has also exposed organizations to a host of vulnerabilities. From cyberattacks targeting remote workers’ devices to the challenges of securing sensitive data across multiple locations, the need for innovative tools and strategies to combat these threats has never been greater. In this article, we will explore some cutting-edge solutions that are revolutionizing the field of remote work security, providing businesses with peace of mind in an increasingly interconnected world.
The rise of remote work and its vulnerabilities
As remote work becomes the new norm, companies and employees are reaping many benefits such as increased flexibility and improved work-life balance. However, this shift also brings with it vulnerabilities that were not as prominent in traditional office settings. One of the main concerns is the increased risk of cyber attacks and data breaches. Remote workers often rely on personal devices and home networks, which may not have the same level of security measures as company-owned equipment and networks. This creates a potential entry point for cybercriminals who can exploit weak passwords or unsecured Wi-Fi connections to gain access to sensitive information.
Another vulnerability that arises from remote work is the potential for decreased collaboration and communication among team members. In a physical office space, colleagues can easily gather around a whiteboard or have impromptu discussions by each other’s desks. However, in a remote setting, these spontaneous interactions are lost unless deliberate efforts are made to recreate them digitally. Without effective tools and strategies in place to facilitate virtual collaboration, teams can struggle to maintain strong communication channels which may negatively impact productivity and overall team performance.
The rise of remote work presents both opportunities for growth and challenges that must be addressed head-on. With cybersecurity threats on the rise and potential breakdowns in team collaboration looming, it is crucial for companies to invest in technologies that can mitigate these vulnerabilities effectively.
Vulnerabilities in remote work infrastructure
The rise of remote work has undeniably opened up new opportunities for flexibility and productivity. However, it has also given rise to a host of vulnerabilities in the infrastructure that supports it. One major concern is the increased likelihood of cyberattacks targeting remote workers. With employees accessing company networks and sensitive data from their personal devices or unsecured Wi-Fi networks, hackers have found a new avenue to exploit. This highlights the urgent need for organizations to prioritize cybersecurity measures and ensure that employees are equipped with the necessary tools and knowledge to protect themselves and their work.
Another vulnerability lies in the lack of physical security when working remotely. Unlike traditional office settings, remote workers often find themselves outside the secure confines of their workplace’s premises. This leaves them susceptible to theft or unauthorized access to their devices or confidential information. Organizations should address this risk by implementing robust identity verification methods, device encryption, and secure file sharing protocols. It is also crucial for employees to be vigilant about physical security practices such as locking devices when not in use and being mindful of public spaces where confidential information could be easily compromised.
Overall, while remote work offers numerous advantages, it also introduces unique vulnerabilities that must be addressed proactively by both organizations and individual employees. By adopting comprehensive cybersecurity measures and encouraging responsible work practices even outside traditional office environments, businesses can better protect themselves against potential threats in today’s increasingly interconnected world.
New tools to enhance remote work security
In today’s rapidly evolving digital landscape, remote work has become an essential part of many organizations’ operations. However, this newfound flexibility also comes with its fair share of security vulnerabilities. With cyber threats becoming increasingly sophisticated, it is crucial for businesses to stay ahead of the curve by implementing new tools like residential proxy that enhance remote work security.
One such tool gaining traction in the industry is Zero Trust Network Access (ZTNA). Unlike traditional VPNs that grant full access to a network upon authentication, ZTNA takes a more granular approach by granting access on an as-needed basis. By adopting a zero-trust mindset and continuously authenticating users and devices before granting access, ZTNA significantly reduces the risk of unauthorized entry or breaches. In addition to VPNs, remote workers often need to share files and documents with their colleagues. Unfortunately, these files can be quite vulnerable to security breaches. This is where secure remote access solutions play a crucial role. Remote access tools such as TSplus offer advanced security features that enable individuals to access remote desktops and other resources seamlessly and securely.
Another innovative tool that organizations are utilizing to enhance remote work security is Cloud Access Security Brokers (CASBs). CASBs act as intermediaries between cloud service providers and users, providing real-time visibility into data usage and enforcing policies based on predefined rules. By monitoring all user activity across various cloud applications and platforms, CASBs help detect any abnormal behavior or potential security risks.
By leveraging these new tools to combat remote work vulnerability, businesses can better protect their sensitive data from ever-evolving cyber threats. With each passing day, it becomes crucial for organizations to adapt to these technological advances in order to ensure the security of their remote workforce and maintain business continuity in an increasingly interconnected world.
Multi-factor authentication for remote access
Multi-factor authentication (MFA) has become an essential tool in today’s remote work landscape, providing an extra layer of security for accessing sensitive information. With the rise of cyber threats and the increasing number of remote workers, relying solely on a username and password is no longer sufficient to protect valuable data from unauthorized access. MFA adds another level of complexity by requiring additional factors for authentication, such as a fingerprint scan, voice recognition, or one-time passcode.
What sets MFA apart from traditional login methods is its ability to provide a more personalized and dynamic approach to identity verification. Rather than relying on static credentials that can be easily compromised or shared among individuals, MFA ensures that only authorized users with specific attributes can gain access. By integrating multiple factors into the authentication process, organizations greatly reduce the risk of breaches caused by weak or stolen passwords alone.
Moreover, implementing MFA not only enhances security but also creates a culture of accountability and awareness among employees. When individuals are required to go through multiple steps to prove their identity before accessing company resources remotely, they become more conscious about the importance of safeguarding their own personal accounts as well. This increased awareness can lead to better cyber hygiene practices overall, ultimately minimizing potential vulnerabilities within the organization’s network.
In conclusion, multi-factor authentication is undoubtedly an essential tool in combating remote work vulnerability. By implementing this robust method for verifying identities in addition to traditional username-password combinations, organizations can significantly reduce the risk of unauthorized access and data breaches. Furthermore, leveraging MFA
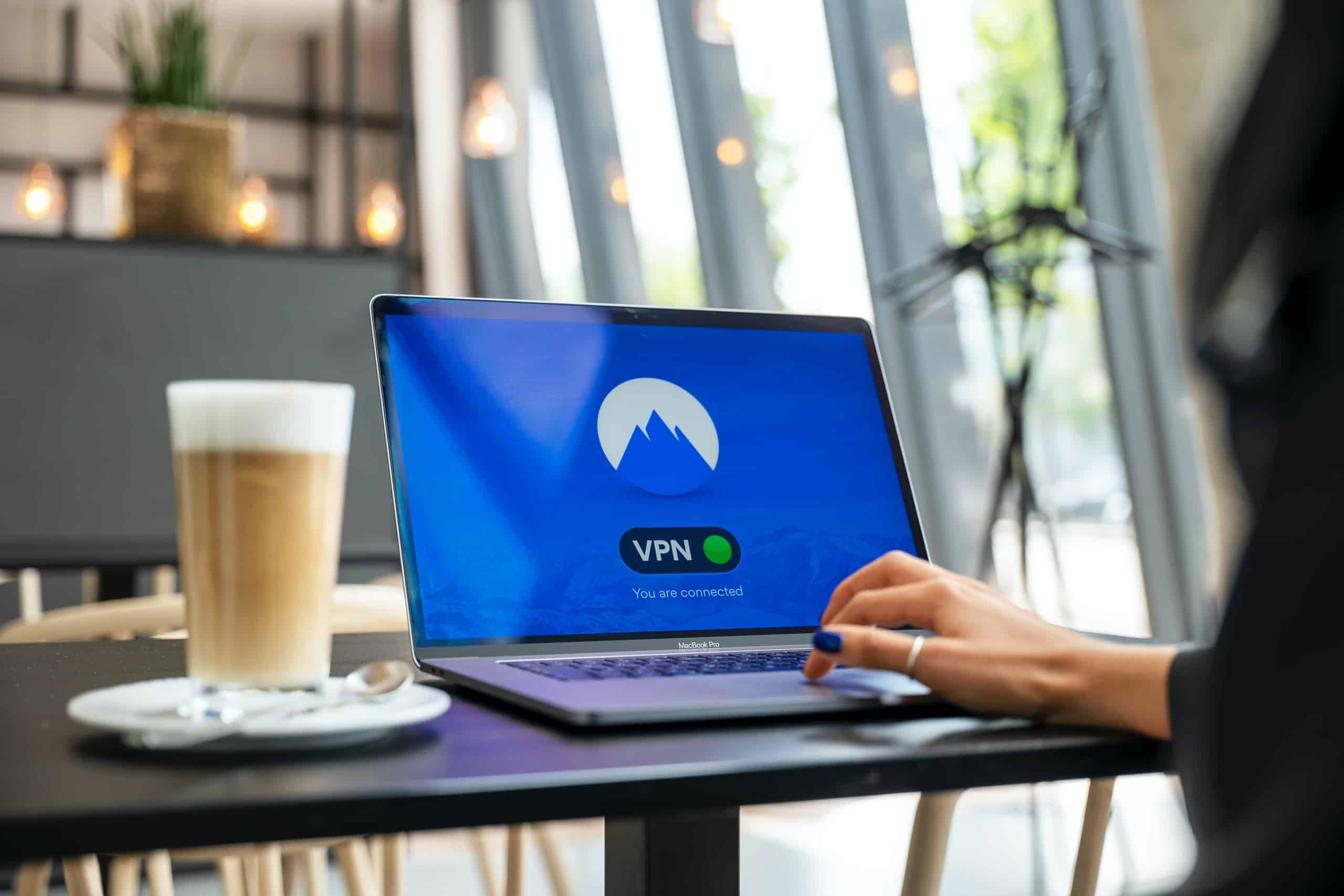
VPNs for secure remote connections
VPNs, or Virtual Private Networks, have become the go-to solution for ensuring secure remote connections in an increasingly digital world. With more businesses and individuals relying on remote work, the need for a reliable and robust VPN has never been greater. Beyond simply encrypting internet traffic, a well-configured VPN provides additional layers of security that safeguard sensitive data from potential threats.
One key aspect of a VPN is its ability to mask your IP address, making it virtually impossible for anyone to trace your online activities back to you. This not only protects your privacy but also shields against potential cyberattacks by malicious actors seeking to exploit vulnerabilities in public networks. Moreover, using a VPN allows you to bypass geo-restrictions and access region-locked content or services. This can be particularly beneficial when traveling abroad or working remotely from different locations.
In addition to security benefits, utilizing a VPN can also optimize network performance by reducing latency and improving bandwidth utilization. By routing internet traffic through an encrypted tunnel, VPNs effectively create a direct connection between your device and the destination server. This minimizes any potential bottlenecks or congestion that may occur when accessing resources over public networks. As more organizations embrace remote work as a long-term solution, implementing robust VPN solutions should be a top priority for protecting sensitive information and optimizing productivity in today’s digital landscape.
Endpoint protection to defend against cyber threats
Endpoint protection is a crucial component in defending against the ever-evolving landscape of cyber threats. With the rise of remote work, endpoints have become even more vulnerable to attacks, making it essential for organizations to invest in robust endpoint security solutions. These solutions not only protect endpoints from malware and viruses but also provide real-time threat intelligence and proactive monitoring.
One emerging trend in endpoint protection is the use of artificial intelligence (AI) and machine learning algorithms. These technologies can analyze large amounts of data to identify patterns and anomalies that may indicate a potential cyber attack. By continuously learning from new threats, AI-powered endpoint protection tools can stay one step ahead of sophisticated hackers.
Another important aspect of endpoint protection is the ability to enforce security policies across all devices, regardless of their location or network connection. This becomes particularly challenging with remote work setups where employees use personal devices or connect through unsecured networks. Endpoint protection solutions should include features such as advanced encryption, secure remote access, and multi-factor authentication to safeguard sensitive data and prevent unauthorized access.
In conclusion, investing in robust endpoint protection is crucial for organizations looking to defend against cyber threats in today’s remote work environment. The use of AI-powered tools can help detect and respond to emerging threats while enforcing strict security policies across all endpoints ensures comprehensive protection. As the threat landscape continues to evolve, adopting cutting-edge technologies and strategies will be key in staying ahead of cybercriminals.
Conclusion: Strengthening the security of remote work
In conclusion, strengthening the security of remote work is crucial in today’s increasingly digitized world. While remote work offers flexibility and convenience, it also presents new challenges that can compromise sensitive data and information. By implementing robust security measures, organizations can minimize the risk of data breaches and cyber-attacks.
One key aspect of strengthening remote work security is ensuring that employees have access to secure networks and devices. Encouraging the use of Virtual Private Networks (VPNs) adds an extra layer of protection by encrypting internet traffic and hiding users’ IP addresses. Additionally, organizations should provide employees with company-approved devices that are regularly updated with the latest security patches and software upgrades.
Furthermore, educating employees about best practices for online security is essential. This includes implementing strong password policies, promoting awareness about phishing scams, and training staff on identifying suspicious emails or attachments. Regular security awareness training sessions can help keep employees vigilant and empower them to make informed decisions when it comes to protecting sensitive information.